Think of a network security assessment as a deep, comprehensive health check for your company's entire digital footprint. Its main purpose is to proactively find and fix security weaknesses before a hacker or malicious actor gets the chance to exploit them. It's all about shifting your security mindset from reactive damage control to a strategic, forward-thinking defense.
Why Network Security Assessments Matter

Imagine your business network is a large building with dozens of doors, windows, and other access points. A network security assessment is the process of methodically checking every single one of those entry points. You're testing the locks, inspecting the cameras, and making sure your security team—your firewalls and response plans—knows exactly what to do if someone tries to get in.
This isn't just about spotting the obvious flaws. A good assessment means learning to see your entire security setup from an attacker's point of view.
This proactive approach is no longer a "nice-to-have." The global market for security assessments, valued at nearly USD 1.97 billion, is expected to skyrocket to over USD 16.6 billion by 2033. This boom is a direct response to the non-stop wave of cyberattacks, which included over 493 million ransomware attempts in just one recent year. The numbers don't lie; a reactive strategy just doesn't cut it anymore.
It's an Investment, Not an Expense
Looking at a network security assessment as just another line item on a budget is a serious misstep. It’s a foundational investment in your business’s resilience and its ability to keep the lights on. By rooting out vulnerabilities before they lead to a data breach or system failure, you're shielding your organization from what could be devastating financial losses and reputational harm.
A successful assessment delivers a clear, prioritized roadmap for improvement. It turns vague, abstract risks into concrete, actionable steps. This allows your IT and security teams to focus their time and money where it will have the biggest impact on your overall security.
A well-executed assessment is a core part of any mature security program. It helps you:
- Prevent Data Breaches: Find and patch the holes in your digital walls that attackers are actively looking to exploit.
- Meet Regulatory Compliance: Give auditors and regulators solid proof that you're meeting industry standards like HIPAA, GDPR, or SOC 2.
- Improve Security ROI: Make sure your security budget is spent fixing the most critical issues first, not on flashy tools that don't address your specific risks.
The table below breaks down the core components of an assessment and why they are so vital for any modern business.
Core Components of a Network Security Assessment
| Pillar | Objective | Business Impact |
|---|---|---|
| Vulnerability Identification | To find and document security flaws in systems, software, and configurations. | Reduces the likelihood of a data breach, preventing financial loss and reputational damage. |
| Threat Modeling | To understand who might attack you and how, based on your industry and data. | Enables a targeted defense strategy, focusing resources on the most probable attack vectors. |
| Compliance Verification | To ensure your security controls meet the requirements of relevant regulations (e.g., GDPR, HIPAA). | Avoids costly fines and legal penalties while building trust with customers and partners. |
| Risk Prioritization | To rank identified vulnerabilities by severity and potential business impact. | Ensures that the most critical issues are addressed first, maximizing the ROI of security efforts. |
Ultimately, a strong assessment gives you the hard data and clear direction needed to make intelligent, risk-informed decisions that protect your bottom line.
Building a Foundation for Risk Management
At the end of the day, the findings from these assessments are the bedrock of your company's risk management strategy. It’s helpful to understand different risk management framework examples, because the data from your assessment feeds directly into how you classify and handle threats.
It gives you the hard evidence needed to justify security projects and prove due diligence to your board, customers, and partners.
Before you jump into the different types of assessments, it pays to have a plan. For anyone getting ready for this process, our detailed https://www.telcosolutions.net/2025/07/27/network-assessment-checklist/ provides a step-by-step guide to ensure you cover all your bases. This kind of methodical preparation is the key to getting real value from your assessment.
Exploring the Core Types of Assessments

Here's the thing: "network security assessment" isn't a one-size-fits-all term. It's actually an umbrella for several different activities, and each one has its own purpose, scope, and level of intensity. Picking the right one boils down to what you're trying to accomplish—are you hunting for known weaknesses or testing your team's live defenses?
To make it simple, let's think of your company network as a secure building. There are really three ways to check its security, and each one maps directly to a core type of assessment. Getting these differences straight is the first step toward making a smart investment in your security posture.
Let's break down the three main types so you can figure out what your organization actually needs.
Vulnerability Assessments: The Systematic Checkup
A vulnerability assessment is like walking the perimeter of your building and methodically checking every single door and window. You aren't trying to pick the locks or smash the glass. You're just looking for anything that’s already unlocked or has a known, factory-default weakness.
The goal here is breadth over depth. We use automated scanning tools to sweep across your entire network, flagging known vulnerabilities, unpatched software, and common configuration mistakes. It’s a high-volume, low-intensity check designed to give you a comprehensive list of potential gaps.
A vulnerability assessment is fundamentally a discovery process. It answers the question, "What are our known weak points?" The output is typically a long list of vulnerabilities, which are then prioritized based on severity scores (like CVSS) so your team knows what to fix first.
Think of this as your routine security checkup. It’s an essential practice that helps you maintain good security hygiene by closing the most obvious and easily exploited holes before an attacker finds them.
Penetration Testing: The Real-World Attack Simulation
If a vulnerability scan is just checking for unlocked doors, a penetration test (or "pen test") is when you hire a team of skilled ethical hackers to actively try to break in. They’ll jiggle handles, pick locks, and maybe even try to trick an employee into holding the door open for them.
This is a goal-oriented, hands-on engagement. Instead of just finding vulnerabilities, pen testers work to exploit them to see just how far they can get. Their objective might be to steal specific data, get admin-level control over a server, or access a critical database.
This process answers a totally different question: "Can an attacker breach our defenses, and what damage could they do?" The human element is what makes all the difference. While automated tools are part of the kit, the real value comes from the creativity and persistence of the testers, who can chain together multiple minor weaknesses to create a major breach—something a simple scanner would never see.
Security Audits: The Compliance Verification
Finally, a security audit isn't about checking locks or trying to break in at all. It's like having a certified inspector show up with a clipboard and the official rulebook. Their only job is to verify that your team is following all the required procedures for locking up the building each night.
An audit is not a technical test; it's a procedural review. Auditors will pour over your documentation, interview your staff, and review system logs to make sure your security controls are aligned with a specific standard or regulation.
The whole point of a security audit is to prove compliance. It answers the question, "Are we following the rules we're supposed to be following?" This is absolutely critical for any organization that has to stick to strict regulatory frameworks, such as:
- HIPAA: For protecting sensitive patient health information.
- PCI DSS: For securing credit card and payment data.
- SOC 2: For service organizations that manage customer data.
The outcome isn't a list of technical flaws but a formal report confirming your compliance status—something often required by partners, clients, and regulators. Choosing the right assessment is the first step in a successful network security assessment program.
Key Methodologies for Effective Assessments

Now that we've covered what a network security assessment is, let's get into the how. A top-tier network security assessment isn't some free-for-all where technicians just start poking around. It’s a structured, repeatable process.
Think of it like an architect's blueprint for a skyscraper. These established frameworks and methodologies ensure that nothing critical gets missed, turning a hugely complex technical project into something manageable and predictable. They create a common language that everyone—from your IT pros on the ground to the C-suite—can understand.
The market backs this up. Network security assessments make up the lion's share of a security services market valued at roughly USD 4.54 billion, which is expected to soar to nearly USD 27.07 billion by 2031. That massive growth isn't just about rising cyber threats; it’s about the growing demand for methodical, proven ways to fight back.
Foundational Security Frameworks
Frameworks are your guiding philosophy. They don't dictate the exact tools you'll use, but they define the big-picture goals of a mature security program. If you're wondering where to begin, two frameworks stand out as industry cornerstones.
NIST Cybersecurity Framework (CSF)
The NIST CSF is widely seen as the gold standard for a reason. It’s not a rigid checklist but a flexible guide that helps you manage and shrink your cybersecurity risk. The entire framework is built around six core functions:
- Govern: This is the high-level strategy—setting the policies and risk management expectations for the whole organization.
- Identify: You can't protect what you don't know you have. This means understanding your assets, business environment, and existing risks to set priorities.
- Protect: Implementing the actual safeguards needed to keep your critical services running.
- Detect: Putting the systems in place to spot a cybersecurity event the moment it happens.
- Respond: Taking swift, decisive action once an incident is detected.
- Recover: Having a plan to get back on your feet and restore your capabilities after an attack.
CIS Controls (Center for Internet Security)
If NIST is the philosophy, the CIS Controls are the actionable to-do list. They offer a prioritized set of defensive measures that are celebrated for their clarity. The controls are split into Implementation Groups (IGs), which is fantastic for businesses of all sizes. You can start with the essentials (IG1) and then climb to more advanced protections (IG2 and IG3) as your security program matures.
The Standard Phases of an Assessment
While frameworks give you the "why," the assessment itself follows a clear, multi-stage process. This phased approach ensures every network security assessment is thorough, from initial planning all the way to the final report.
An assessment without a clear process is like a ship without a rudder. Following established phases ensures you move from discovery to resolution efficiently, turning raw data into meaningful security improvements.
Let’s walk through the typical lifecycle of a comprehensive assessment.
1. Planning and Scoping
This is, without a doubt, the most important stage. Get this wrong, and the rest of the project is at risk. Here, you define the "rules of engagement": what gets tested, when it gets tested, and—just as important—what's off-limits. Clear communication with every stakeholder is non-negotiable to set objectives and lock down which assets are most critical.
2. Information Gathering and Discovery
With the scope locked in, the real detective work begins. This phase, often called reconnaissance, is all about mapping the target network. The team identifies live hosts, open ports, and running services to build a complete picture of the network's attack surface. You have to know the terrain before you can defend it.
3. Vulnerability Analysis and Exploitation
With a map of the network in hand, the team starts probing for weaknesses. This can be anything from running automated vulnerability scanners to attempting manual exploits, like you’d see in a full-blown penetration test. Every potential flaw is carefully documented and verified to make sure it's a real threat, not just a false positive.
For a deeper dive into how this looks in practice, an email security audit checklist can offer great, specific examples.
4. Reporting and Remediation
Finally, all the technical findings are translated into a clear, actionable report. This document doesn't just list problems; it prioritizes them based on risk and provides concrete, step-by-step recommendations for fixing them. The goal is to empower decision-makers to focus resources where they matter most, a vital part of any effective enterprise network security solutions.
Your Step-by-Step Assessment Guide
Jumping into a network security assessment can feel like a huge undertaking. But if you break it down into a clear, step-by-step process, it becomes a much more manageable project. This guide walks you through the essential stages, from planning all the way to the final report, making sure you get real security improvements out of your investment.
This approach ensures that whether you use an in-house team or bring in an outside partner, the results are clear, measurable, and directly linked to making your defenses stronger. It turns the big idea of an "assessment" into a concrete project with a clear start, middle, and end.
Stage 1: Define Your Objectives and Scope
Before you even think about launching tools or scanning systems, the most important work happens: planning. This is where you have to answer the big question: "What are we actually trying to accomplish here?" Your answer will shape the entire project. Are you getting ready for a compliance audit, hunting for a specific type of vulnerability, or stress-testing your incident response plan?
Once your goal is clear, it's time to define the scope. This means taking a hard look at all your network assets—servers, databases, applications, cloud environments—and deciding which ones are on the table for this assessment. You absolutely have to identify the critical systems that handle sensitive data or keep the business running. Just as important is defining what's out-of-scope to keep the project focused and avoid causing unnecessary disruptions.
Stage 2: Choose Your Team and Tools
With a clear scope in hand, your next decision is about who will do the work. You can task your internal IT or security team, or you can hire a specialized third-party firm. An internal team knows your environment inside and out, but an external partner brings a fresh, unbiased perspective and often has specialized skills that can spot issues your own team might have missed.
The choice between an internal and external team isn't just about cost; it's about perspective. An external team acts like a visiting inspector who has seen hundreds of different buildings, noticing subtle flaws an in-house manager, who walks the halls every day, might no longer see.
No matter who's running the show, they'll need the right tools for the job. This usually involves a mix of:
- Vulnerability Scanners: Automated tools that check for known weaknesses and common misconfigurations.
- Network Mapping Tools: Software to visualize your network layout and identify every connected device.
- Exploitation Frameworks: Used in penetration tests to simulate how a real-world attacker would operate.
- Packet Analyzers: Tools that let you look inside your network traffic to spot suspicious activity.
Stage 3: Execute the Assessment
Now it’s time to get hands-on. This is where the actual testing begins. Sticking to the "rules of engagement" you established during the scoping phase, the assessment team will start methodically probing your network. This involves gathering information, scanning for vulnerabilities, and—if it's a penetration test—actually trying to exploit them.
Throughout this phase, documentation is everything. Every finding, every attempted exploit, and every system response needs to be logged meticulously. This data becomes the hard evidence for the final report and guarantees that every risk you identify can be validated and reproduced later.
This graphic shows the critical compliance and reporting workflow that kicks in right after the technical work is done.
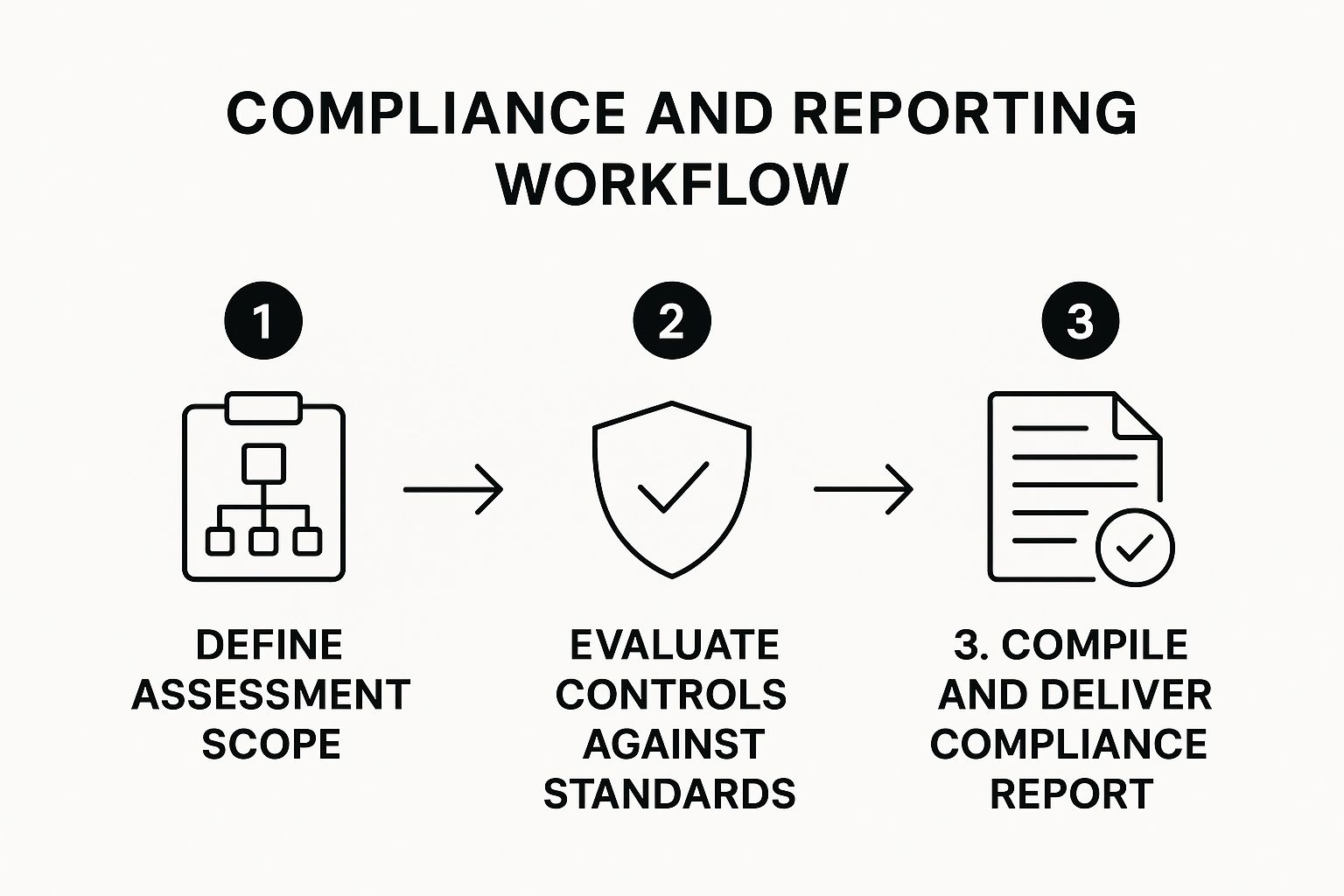
The flow illustrates how an assessment narrows down from a broad scope to a focused evaluation against specific standards, leading to a report you can actually use.
Stage 4: Analyze Findings and Plan Remediation
Once the testing is over, all the raw data gets analyzed to build a clear picture of your security posture. This isn't just about generating a long list of problems. The findings have to be prioritized based on what they mean for the business. A risk matrix, which weighs the likelihood of a vulnerability being exploited against its potential damage, is a fantastic tool for this. It helps you tell the difference between a minor issue and a critical flaw that could bring your operations to a halt.
The final deliverable should be a comprehensive remediation plan. This is your actionable roadmap, detailing each vulnerability, assigning it a risk level, and providing clear, step-by-step instructions on how to fix it. This demand for clear, actionable reporting is fueling huge growth in the field. In the United States alone, the network security market was valued at USD 5.3 billion and is projected to more than double to USD 11.6 billion by 2033. You can learn more about the trends shaping the US network security market and see why effective threat management is such a hot-button issue.
Maximizing Your Assessment ROI
A detailed report from a network security assessment is a powerful tool, but its value disappears if it just sits on a server collecting digital dust. Let's be honest: the real return on investment isn't in the document itself. It's in the tangible security improvements that follow.
To get the most from your efforts, you have to treat the assessment not as a final exam, but as the first chapter in an ongoing security story. It’s a mindset shift from a one-and-done project to a continuous improvement cycle. Your business is always in flux—new employees come on board, new software gets deployed, and new services are spun up in the cloud. A single assessment is just a snapshot; its findings can become outdated surprisingly fast.
Adopt a Continuous Assessment Cycle
High-performing organizations don’t just "do" an assessment; they build a program around it. They treat network security assessments as a cyclical process, creating a rhythm of testing, fixing, and re-testing that keeps pace with their evolving attack surface.
This continuous model usually involves a few key activities:
- Scheduled Assessments: Run comprehensive assessments at regular intervals, like annually or semi-annually. This establishes a consistent security baseline to measure against.
- Trigger-Based Testing: Kick off targeted assessments after significant changes, such as a major system upgrade, a new application launch, or integrating a new cloud service.
- Ongoing Monitoring: Supplement those periodic deep dives with continuous automated scanning. This helps you catch new vulnerabilities the moment they appear.
Following a strategy like this ensures your security posture doesn't just get strong—it stays strong.
The goal is to move beyond a simple compliance checklist and build a culture of proactive security. An assessment shouldn't just be about passing an audit; it should be about genuinely reducing business risk day in and day out.
Integrate Findings into Your Risk Management Program
An assessment report can feel intensely technical, full of vulnerability scores and system-level jargon. To get the resources you need for remediation, you have to translate those technical findings into business impact. After all, a critical vulnerability on a non-essential test server carries far less weight than a moderate one on the server processing all your customer payments.
This is where your broader risk management program comes into play. Each weakness you find must be put into context: What’s the real-world risk to the business if this flaw is exploited? Could it lead to a data breach, operational downtime, or regulatory fines? To better understand how identifying and mitigating these issues protects the business, it's helpful to review a detailed guide to risk management for businesses.
By framing the conversation around business risk, you can secure executive buy-in much more effectively. When decision-makers see a clear line connecting a technical fix to protecting revenue and reputation, they are far more likely to approve the necessary budget and personnel. This turns the remediation plan from an IT "ask" into a strategic business priority, delivering a true return on your assessment investment through measurable risk reduction.
Common Assessment Pitfalls to Avoid
Even the most carefully planned network security assessments can miss the mark. Understanding where others have gone wrong is one of the best ways to make sure your investment of time and money actually pays off with strong, actionable results.
Falling into these common traps can completely undermine an assessment's value, leaving your organization with a dangerous false sense of security.
The most frequent—and damaging—mistake is poor scoping. This happens when the planning phase doesn't correctly identify and prioritize your most critical assets. The result? Your assessment team wastes time poking at low-impact systems while your true crown jewels, like databases full of sensitive customer data, are completely ignored. A proper assessment always starts with a rock-solid asset inventory.
Another huge pitfall is relying too heavily on automated tools. Don't get me wrong, scanners are essential for spotting known vulnerabilities across a wide attack surface. But they have zero human intuition or business context. An automated tool can't connect the dots between several low-level flaws to orchestrate a major breach, nor can it understand which vulnerabilities pose the biggest threat to your specific business.
Forgetting the Human Element
A purely automated approach just doesn't see the whole picture. Security isn't just a tech problem; it's a human one. A scanner can’t tell you that your password policy is weak or that a specific department is dangerously susceptible to phishing attacks. This is exactly why you need a balanced approach that pairs automated scanning with manual, expert-led testing and procedural reviews.
A network security assessment should never be a "fire and forget" automated scan. The real value comes from expert analysis that contextualizes technical findings within your unique business environment, turning raw data into strategic intelligence.
This human-centric analysis helps avoid another common failure: delivering reports that are way too technical for the people who need to sign the checks. A 100-page report dripping with jargon is completely useless to a CFO or CEO. The findings have to be translated into clear business language that focuses on risk and potential financial impact.
Common Mistakes and Their Solutions
To ensure your next network security assessment is a genuine success, make sure to steer clear of these all-too-common missteps:
- Pitfall – Ignoring Business Context: Focusing only on technical vulnerabilities without thinking about how they could impact the business.
- Solution: Use a risk matrix to prioritize what you find. A medium-severity flaw on a critical e-commerce server is far more important than a high-severity one on a non-essential dev machine.
- Pitfall – Treating it as a One-Time Event: Running an assessment once and thinking you're good to go for the next few years.
- Solution: Put a continuous assessment cycle in place. For more on this, our guide on network monitoring best practices offers some great insights into maintaining constant visibility.
- Pitfall – Creating an Unactionable Report: Handing over a dense, technical document that lacks clear, prioritized steps for fixing things.
- Solution: The final report needs an executive summary that speaks directly to business risk, along with a detailed, step-by-step remediation plan for your technical team.
Avoiding these pitfalls is what transforms an assessment from a simple compliance checkbox into a strategic tool for real, measurable risk reduction.
A Few Common Questions, Answered
Even with a solid plan, it's natural for a few questions to pop up when you're getting ready for a network security assessment. Let's tackle some of the most common ones we hear from business leaders to clear things up before you start.
How Often Should We Conduct Assessments?
There's no single magic number here—the right frequency really depends on your business. The big things to consider are your industry's compliance rules, how much you rely on your digital systems, and how quickly your IT environment is changing.
As a general rule of thumb, a comprehensive assessment at least annually is a smart baseline. But you'll want to ramp that up for your most critical systems. It’s also wise to test immediately after any major changes, like rolling out a new app or moving services to a new cloud provider.
What’s the Difference Between an Assessment and an Audit?
People often mix these two up, but they serve very different purposes. It's easy to get them confused, but the distinction is crucial.
Think of it this way: an assessment is about finding technical weak spots, while an audit is about checking if you're following the rules.
An assessment is a hands-on, technical deep-dive to find vulnerabilities. It answers the question, "What's broken?" An audit is a procedural review against a specific standard, answering, "Are we compliant?"
Here’s how they break down:
- Assessment: This is a technical, hands-on hunt for security flaws. The goal is to uncover and prioritize real-world risks before an attacker does.
- Audit: This is a structured checkup to make sure your organization is sticking to a specific set of policies or regulations, like HIPAA or PCI DSS.
How Much Does a Network Security Assessment Cost?
The cost of a network security assessment can swing pretty widely. The final price really comes down to three main things: the size and complexity of your network, the depth of the assessment you need, and the provider you partner with.
For instance, a full-on penetration test will naturally cost more than a simple automated vulnerability scan because it requires a lot more hands-on expertise and time. The price could be a few thousand dollars for a basic scan at a smaller company or jump into the tens of thousands for a deep, enterprise-wide assessment. Your best bet is always to get quotes based on a clearly defined scope of work to get an accurate picture of the investment.
At TelcoSolutions, we help you build a resilient and secure network foundation. We connect businesses with over 300 providers to ensure you have the right mix of telecom and network services to thrive. Find the best tools for your business at the best rate.

